Jay Patel, Security Operations Lead at Prospa, shares six tips for protecting your small business from cyber attacks.
At a glance
Here’s a snapshot of the advice from Jay Patel, Security Operations Lead at Prospa:
- Be alert to the ways cyber attackers can exploit an emotional response by demanding a swift response or hefty payment.
- If an email doesn’t seem quite right, pick up the phone before responding.
- Implement added layers of security via two-factor authentication and password managers.
- Practise good IT hygiene, and don’t put off making updates and backups.
As much as we might not like thinking about cybercrime, it presents a real risk to small businesses.
The Australian Cyber Security Centre (ACSC) found that during the 2022-2023 financial year, small businesses on average lost $46,000 due to cybercrime. They also made more cybercrime reports than in the previous financial year.
Fortunately, there are straightforward and cost-effective ways small business owners can help protect themselves from breaches.
Start with these six practices to give your business a head start in improving your cybersecurity.
1Be alert to social engineering
Social engineering, commonly known as phishing, refers to cyber attacks that play on emotional responses to manipulate people into divulging sensitive information.
Consider an email that demands payment of a bill within 24 hours or services will be cut off, or threatens the possibility of (fake) legal action if you do not respond.
According to the ACSC, attackers can use a range of strategies to trick you, including:
- Is the message claiming to be from someone official?
- Are you told you have a limited time to respond?
- Does the message make you panic, fearful, hopeful or curious?
- Is the message offering something that seems too good to be true?
The financial industry is seeing more instances of bank and invoice fraud done via phishing, and small business owners can be vulnerable targets. For instance, attackers can use one of your supplier emails and ask you to update their bank account details – meaning the next payment goes into the attacker’s bank account.
Invoice fraud is when criminals compromise a vendor’s email account and change the bank details on the company’s invoices. The customer pays the invoice, thinking they are paying the vendor, but instead sends the money to the attacker’s bank account.
So how do you protect yourself? You could:
- Pick up the phone to ensure legitimacy. If something sounds too good to be true, it probably is. A quick call that saves a $20,000 invoice being paid to the wrong account is time well spent.
- Educate your staff. Phishing is no longer just the promise of millions of dollars. Attackers can also find success in sending emails that appear to fit into the context of your day-to-day operations. By embedding a level of caution into your processes and your culture, however, you’ll go a long way to protect your business.
- Report malicious emails as spam. The more people report phishing emails, the better service providers get at managing filters and security settings.
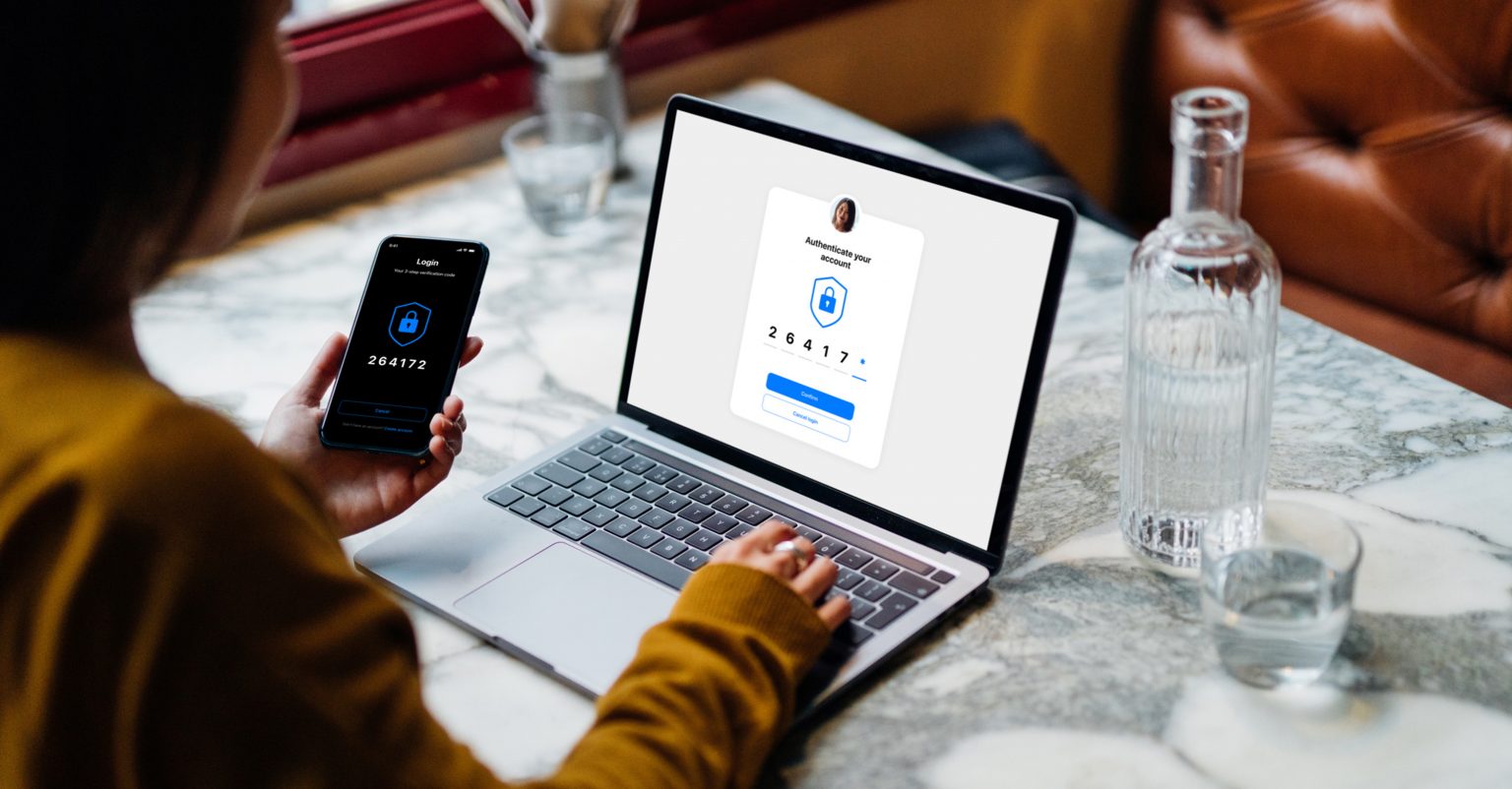
2Use two-factor authentication
Two-factor authentication (2FA) adds an extra layer of security to your online accounts. It works by requiring you to enter an additional credential – usually a code provided via email, SMS or authenticator app – after you’ve entered your username and password. Many applications already have a 2FA option you can enable.
2FA is an effective way not only to protect your own data but also to show your customers that you take the protection of their data seriously.
Codes received via SMS do the job, but with sim swapping on the rise, an authenticator app raises the bar even higher by generating codes that change every minute. There are plenty of free ones available.
3Use a password manager
Despite it being bad practice, many people still use one password across all their different accounts, from email and social media to bank accounts and apps. If one password is all that stands between you and all your personal and financial data, you’re not putting up enough of a barrier.
Use a password manager to generate strong, random and long passwords, and store them securely so you never have to remember them. Password managers are easy to set up and use across your business.
4Update your systems
Notifications to install new updates can be annoying, but they are essential to maintaining good IT hygiene. Updates come with new features and security patches, and should be installed as required across your devices.
Enable automatic updates to make it even easier to stay up-to-date.
5Backup your data
Don’t let backups be an afterthought. You’ll be glad if you suddenly need them because an attacker encrypted your computer or you left a laptop on the train.
A cloud-based service like Google Drive or Dropbox is ideal for always having a real–time copy of your data. Cloud–based computing is often faster, more efficient and more secure than maintaining an on-site server.
Over the years we’ve seen significant data breaches this year that providing an important lessons about the importance of data management. Customer data from Optus, the second largest telecommunications company in the country, was accessed by attackers, affecting up to 10 million Australians.
Personal information such as driver’s licences, Medicare cards and passport numbers were exposed, prompting many to change their details – not something any business large or small wishes to have to notify their customers about.
6Only ask for and keep the data you need
It’s poor form, from both a data security and a customer trust perspective, to hold onto sensitive consumer information if it is no longer necessary. That’s why it’s important to only retain the data you need – data that is essential to business.
In fact, only requesting the data you need in the first place can minimise risk – it’s impossible to leak data you don’t hold.
Doing otherwise could land businesses in hot water if it’s revealed that they have, or could have, mismanaged that data, or left it sitting in the cloud where it remains vulnerable to cyber attack.
For further guidance on upping your business’s cybersecurity, read the ACSC’s small business cybersecurity guide, which can help owners protect themselves from the most common cybersecurity incidents.
How Prospa protects customer data
At Prospa, we take cybersecurity seriously – after all, we protect the data of more than 17,900 small business customers.
Prospa’s dedicated in-house cybersecurity team works to ensure customer data is kept safe and secure, and maintains the tools and systems to do so. Our Product Security function makes sure our products are built securely, and our Security Operations function monitors and responds to potential security threats.
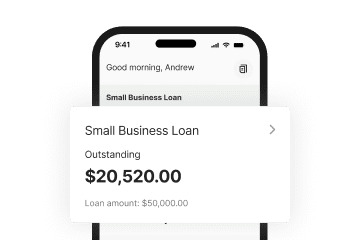
Importantly, we only keep the data we need. For example, when a customer enters their bank account details so Prospa can quickly assess the appropriateness of a loan, we only assess the data required to support that loan process, which enable us to give you an outcome faster, without having the hassle of providing bank statements.
This means we are not provided with your login credentials or passwords, or the ability to access your internet banking. The only data, than is accessed is your banking transaction data linked to that account.
Neither Prospa nor its valued customers would hope for a data breach – that’s why we take precautions to protect that data at all stages of the process. The full details of how we handle your data are covered in our Privacy Policy.
While Prospa is larger than many small businesses and is the guardian of large quantities of customer data, we put into practice all the principles described above: being on alert for suspicious email activity, using 2FA and password managers extensively, and maintaining the utmost IT security hygiene with best practices across the business.
2FA is mandated across all our applications, for example – it’s a key component of our data security policy. If you use the Prospa App, you can also set up biometric security features built into it including facial recognition and touch ID.
This article was originally published in April 2022. In light of recent events in cybersecurity, we’ve updated it to provide further insights to small business owners.
Need flexible access to funds that could help your business grow? Speak with one of our small business lending specialists.